Gnupg Generate Rsa Key Pair
GNU gpg is encryption and signing tool.
- Gnupg Generate Rsa Key Pair Key
- How To Generate Rsa Key Pair
- Gpg Generate Public Private Key Pair
- Generate Rsa Private Key
The GNU Privacy Guard (GnuPG or GPG) is a free software replacement for the PGP suite of cryptographic software.
Oct 01, 2018 It is a free software and pretty straightforward to install. Before you can use it though, you need to create a key pair first and this may be confusing to beginners. Here are the steps to generate a key pair in GPG4Win Kleopatra: Launch Kleopatra and click on New Key Pair.
GnuPG encrypts messages using asymmetric keypairs individually generated by GnuPG users. The resulting public keys can be exchanged with other users in a variety of ways, such as Internet key servers. They must always be exchanged carefully to prevent identity spoofing by corrupting public key ↔ ‘owner’ identity correspondences. It is also possible to add a cryptographic digital signature to a message, so the message integrity and sender can be verified, if a particular correspondence relied upon has not been corrupted.
How do I create my own GnuPG private and public key
- How to: Create a public-private key pair.; 2 minutes to read; In this article. To sign an assembly with a strong name, you must have a public/private key pair. This public and private cryptographic key pair is used during compilation to create a strong-named assembly. You can create a key pair using the Strong Name tool (Sn.exe).
- Mar 14, 2016 This video goes over how to generate either a PGP 9, or NAI7 key pair within FTP Manager. The video also covers the public PGP key export process, to provide a vendor with your key.
- Apr 04, 2017 (y/N) y GnuPG needs to construct a user ID to identify your key. Real name: myname Email address: myname@linoxide.com Comment: my-key-pair You selected this USER-ID: 'myname (my-key-pair) '. You need a Passphrase to protect your secret key. We need to generate a lot of random bytes.
- This will generate a public-private key pair in the GPG keyring and prompt for the size of the encryption key: ELG-E keys may be between 1024 and 4096 bits long. What keysize do you want? (2048) Select the default value of 2048. Enter greater or fewer bits depending on how secure the encryption must be.
1) Login to your shell account
2) Use gpg command to create the keys$ gpg --gen-key
Output:
3) Now keys generated, you can list your own key using:$ gpg -K
OR$ gpg --list-keys
Output:
Gnupg Generate Rsa Key Pair Key
Let us try to understand the line pub 1024D/CA7A8402 2007-02-10:
- pub : Public key
- 1024D : The number of bits in the key
- CA7A8402 : The key ID
- 2007-02-10 : The date of key creation
- Vivek Gite : The user real name
- <vivek@nixcraftcorp.com> : The email id
Most important is the key ID i.e. CA7A8402. Make sure you use powerful passphrase to protect keys and not the easy one.
4) To list secret key, type the command:$ gpg --list-secret-keys
Output:
Most noteworthy, the point is that the separations have managed to founds the tech fans, which can include in utilizing’s in the key management system. Besides, it can also provide the user the loss of time to their customers have a difficult time in the adjustments. Windows 8 pro key generator free download. From this particular and use to make goals and stay away from disappointment and to make everybody from it.
ADVERTISEMENTS
- Table of Contents
- Generating a new keypair
- Exchanging keys
- Encrypting and decrypting documents
- Making and verifying signatures
GnuPG is a tool for secure communication.This chapter is a quick-start guide that covers the core functionalityof GnuPG.This includes keypair creation, exchanging and verifying keys, encryptingand decrypting documents, and authenticating documents with digitalsignatures.It does not explain in detail the concepts behind public-key cryptography,encryption, and digital signatures.This is covered in Chapter 2.It also does not explain how to use GnuPG wisely.This is covered in Chapters 3 and 4.
How To Generate Rsa Key Pair
GnuPG uses public-key cryptography so that users may communicate securely.In a public-key system, each user has a pair of keys consisting ofa
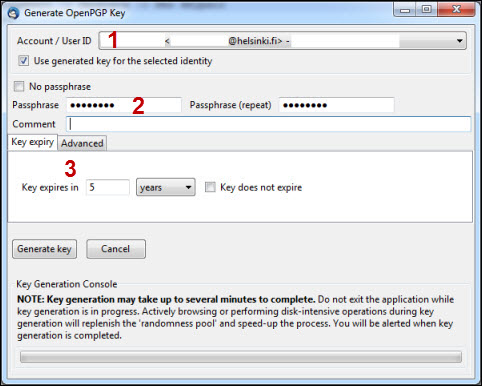
The command-line option
You must also choose a key size.The size of a DSA key must be between 512 and 1024 bits, and an ElGamalkey may be of any size.GnuPG, however, requires that keys be no smaller than 768 bits.Therefore, if Option 1 was chosen and you choose a keysize larger than1024 bits, the ElGamal key will have the requested size, but the DSAkey will be 1024 bits.
Finally, you must choose an expiration date.If Option 1 was chosen, the expiration date will be used for both theElGamal and DSA keypairs.
You must provide a user ID in addition to the key parameters.The user ID is used to associate the key being created with a realperson.
GnuPG needs a passphrase to protect the primary and subordinate private keys that you keep in your possession.
I did this for fun, and now I am done with this. KMS-activator for operating systems Windows VL editions: Vista, 7, 8, 8.1, 10, Server 2008, 2008 R2, 2012, 2012 R2 also Office 2010, 2013, 2016.Important: If you like MS Windows and MS Office please buy legal and original this program help to test this products, but recommend you buy legal from creators (M$ Corp). Working in W8 and Office 2013 fresh install and VOLUME LICENSE editions.Based off of open source code KMS Emulator of mikmik38, jm287, zm0d, CODYQX4.BEFORE ACTIVATION ANY ONE OF THE ITEM. Windows 8.1 activation key generator 2016.
 Generating a revocation certificate
Generating a revocation certificateAfter your keypair is created you should immediately generate a revocationcertificate for the primary public key using the option
Gpg Generate Public Private Key Pair
Notes
Generate Rsa Private Key
[1]Option 3 is to generate an ElGamal keypair that isnot usable for making signatures.