Openssl Generate Public Key From P12
Malwarebytes anti malware premium key generator. OpenSSL provides read different type of certificate and encoding formats. OpenSSL supports certificate formats like RSA, X509, PCKS12 etc. We will look how to read these certificate formats with OpenSSL. Read RSA Private Key. RSA is popular format use to create asymmetric key pairs those named public and private key. OpenSSL – How to convert SSL Certificates to various formats – PEM CRT CER PFX P12 & more How to use the OpenSSL tool to convert a SSL certificate and private key on various formats (PEM, CRT, CER, PFX, P12, P7B, P7C extensions & more) on Windows and Linux platforms.
Express vpn key generator torrent. Mar 31, 2020 Express VPN Premium Crack Full Torrent APK This program causes you to dispose of them and you can do financial transactions, secure browsing, payments and so on over the web. Furthermore, this product gives you 256-bit encryption security. Mar 08, 2020 Express VPN makes it very simple to use a VPN on a router and allows you to switch between server places fast. ExpressVPN is Netflix’s best VPN for 24/7 access to many areas and the most powerful HD streaming network. It is also an excellent torrent VPN with no torrent or bandwidth constraints. Express VPN Crack Torrent Keygen. Mar 18, 2020 Express VPN 7.5.5 Crack + Activation Code With Torrent. Express VPN 7.5.5 Crack is a smart VPN providing software. This tool provides you with safe. Mar 18, 2020 Express VPN Crack Plus Torrent Express VPN 8 Crack is a powerful and excellent software that provides a safe and private network connection by connecting one or more devices together. It is the best VPN tool that becomes simple and very fast. Nov 11, 2019 Express VPN 6.7.1 Crack Full Key With Torrent Download Here! Express VPN Crack is the world’s best VPN (Virtual Private Network) application that gives high speed and ultra-secure internet browsing. It has numerous great features and is also.
- This module allows one to (re-)generate PKCS#12.
The below requirements are needed on the host that executes this module.
- python-pyOpenSSL
| Parameter | Choices/Defaults | Comments |
|---|---|---|
| action string |
| export or parse a PKCS#12. |
| attributes string | The attributes the resulting file or directory should have. To get supported flags look at the man page for chattr on the target system. This string should contain the attributes in the same order as the one displayed by lsattr. The = operator is assumed as default, otherwise + or - operators need to be included in the string. | |
| backup added in 2.8 |
| Create a backup file including a timestamp so you can get the original output file back if you overwrote it with a new one by accident. |
| certificate_path path | The path to read certificates and private keys from. | |
| force |
| Should the file be regenerated even if it already exists. |
| friendly_name string | Specifies the friendly name for the certificate and private key. | |
| group | Name of the group that should own the file/directory, as would be fed to chown. | |
| iter_size integer | Default: | Number of times to repeat the encryption step. |
| maciter_size integer | Default: | Number of times to repeat the MAC step. |
| mode string | The permissions the resulting file or directory should have. For those used to /usr/bin/chmod remember that modes are actually octal numbers. You must either add a leading zero so that Ansible's YAML parser knows it is an octal number (like 0644 or 01777) or quote it (like '644' or '1777') so Ansible receives a string and can do its own conversion from string into number.Giving Ansible a number without following one of these rules will end up with a decimal number which will have unexpected results. As of Ansible 1.8, the mode may be specified as a symbolic mode (for example, u+rwx or u=rw,g=r,o=r).As of Ansible 2.6, the mode may also be the special string preserve.When set to preserve the file will be given the same permissions as the source file. | |
| other_certificates list / elements=path | List of other certificates to include. Pre 2.8 this parameter was called ca_certificates | |
| owner | Name of the user that should own the file/directory, as would be fed to chown. | |
| passphrase string | ||
| path | Filename to write the PKCS#12 file to. | |
| privatekey_passphrase string | Passphrase source to decrypt any input private keys with. | |
| privatekey_path path | ||
| selevel | Default: 's0' | This is the MLS/MCS attribute, sometimes known as the range.When set to _default, it will use the level portion of the policy if available. |
| serole string | When set to _default, it will use the role portion of the policy if available. | |
| setype string | When set to _default, it will use the type portion of the policy if available. | |
| seuser string | By default it uses the system policy, where applicable.When set to _default, it will use the user portion of the policy if available. | |
| src path | ||
| state |
| Whether the file should exist or not. All parameters except path are ignored when state is absent. |
| unsafe_writes boolean |
| Influence when to use atomic operation to prevent data corruption or inconsistent reads from the target file. By default this module uses atomic operations to prevent data corruption or inconsistent reads from the target files, but sometimes systems are configured or just broken in ways that prevent this. One example is docker mounted files, which cannot be updated atomically from inside the container and can only be written in an unsafe manner. This option allows Ansible to fall back to unsafe methods of updating files when atomic operations fail (however, it doesn't force Ansible to perform unsafe writes). IMPORTANT! Unsafe writes are subject to race conditions and can lead to data corruption. |
See also
- openssl_certificate – Generate and/or check OpenSSL certificates
- The official documentation on the openssl_certificate module.
- openssl_csr – Generate OpenSSL Certificate Signing Request (CSR)
- The official documentation on the openssl_csr module.
- openssl_dhparam – Generate OpenSSL Diffie-Hellman Parameters
- The official documentation on the openssl_dhparam module.
- openssl_privatekey – Generate OpenSSL private keys
- The official documentation on the openssl_privatekey module.
- openssl_publickey – Generate an OpenSSL public key from its private key
- The official documentation on the openssl_publickey module.
Common return values are documented here, the following are the fields unique to this module:
| Key | Returned | Description |
|---|---|---|
| backup_file string | changed and if backup is yes | Sample: |
| filename | changed or success | Path to the generate PKCS#12 file. /opt/certs/ansible.p12 |
| privatekey string | changed or success | Path to the TLS/SSL private key the public key was generated from. /etc/ssl/private/ansible.com.pem |
- This module is not guaranteed to have a backwards compatible interface. [preview]
- This module is maintained by the Ansible Community. [community]
Authors¶
- Guillaume Delpierre (@gdelpierre)
Hint
Openssl Generate Public Key From Private Key
If you notice any issues in this documentation, you can edit this document to improve it.
Steps to generate self-signed PKCS#12 SSL certificate and export its keys:
1- Create PKCS#12 keystore (.p12 or .pfx file)
myKeystore.p12= keystore filename. It can with .pfx extension as well.MY_PASSWORD= password used for the keystore and the private key as well.CN= commonName, it will be shown as certiciate name in certificates list.OU= organizationUnit, department name for example.O= organizationName, the company name.L= localityName, the city.S= stateName, the state.C= country, the 2-letter code of the country.
Note: This step can be done using openssl but it's more complicated.
2- Create the public certificate (has the header -----BEGIN CERTIFICATE-----):
Using keytool:
Or using openssl:
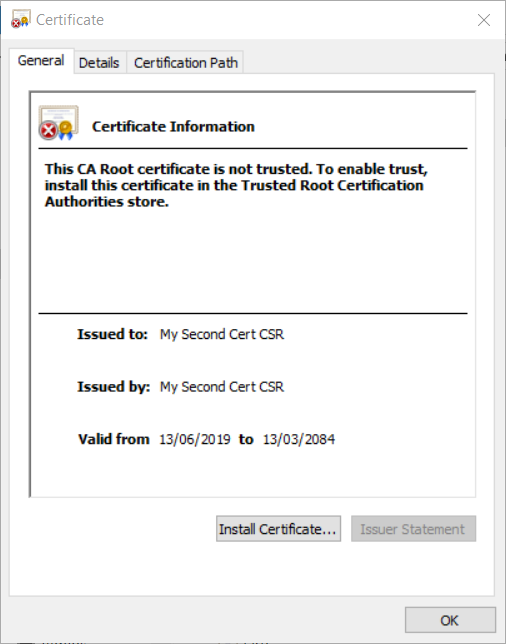
Note: Import public-certificate.pem into browsers to trust it. Add it to 'Trusted Root Certification Authorities' certificate store.
3- Export the private key (has the header -----BEGIN PRIVATE KEY-----):
Openssl Generate Public Key From P12 To Pem
4- Export the public key from the private key (has the header -----BEGIN PUBLIC KEY-----):